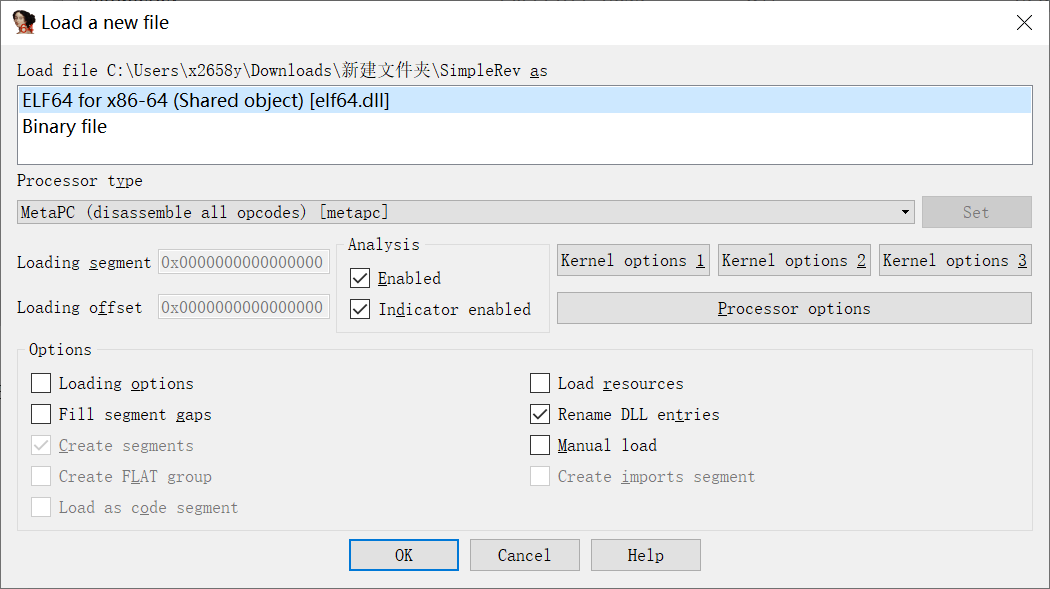
无壳, 直接拖进IDA分析, F5查看伪代码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
| int __cdecl main_0(int argc, const char **argv, const char **envp)
{
size_t v3;
const char *v4;
size_t v5;
char v7;
char v8;
signed int j;
int i;
signed int v11;
char Destination[108];
char Str[28];
char v14[8];
for ( i = 0; i < 100; ++i )
{
if ( (unsigned int)i >= 0x64 )
j____report_rangecheckfailure();
Destination[i] = 0;
}
sub_41132F("please enter the flag:", v7);
sub_411375("%20s", (char)Str);
v3 = j_strlen(Str);
v4 = (const char *)sub_4110BE(Str, v3, v14);
strncpy(Destination, v4, 0x28u);
v11 = j_strlen(Destination);
for ( j = 0; j < v11; ++j )
Destination[j] += j;
v5 = j_strlen(Destination);
if ( !strncmp(Destination, Str2, v5) )
sub_41132F("rigth flag!\n", v8);
else
sub_41132F("wrong flag!\n", v8);
return 0;
}
|
关键在于sub_4110BE()这个函数,
菜鸡一时没看出来它是干啥的. 于是把它从IDA抠出来,
略作修改让它能跑起来, 命名为unknown(), 看看这个它的作用
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
| #include <cstdio>
#include <cstdlib>
#include <cstring>
using namespace std;
void* __cdecl unknown(char* a1, unsigned int a2)
{
int v4;
int v5;
int v6;
int v7;
int i;
unsigned int v9;
int v10;
int v11;
void* v12;
char* v13;
if (!a1 || !a2)
return 0;
v9 = a2 / 3;
if ((int)(a2 / 3) % 3)
++v9;
v10 = 4 * v9;
v12 = malloc(v10 + 1);
if (!v12)
return 0;
memset(v12, 0, v10 + 1);
char byte_41A144[4];
char aAbcdefghijklmn[] = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=\x00";
v13 = a1;
v11 = a2;
v4 = 0;
while (v11 > 0)
{
byte_41A144[2] = 0;
byte_41A144[1] = 0;
byte_41A144[0] = 0;
for (i = 0; i < 3 && v11 >= 1; ++i)
{
byte_41A144[i] = *v13;
--v11;
++v13;
}
if (!i)
break;
switch (i)
{
case 1:
*((unsigned char*)v12 + v4) = aAbcdefghijklmn[(int)(unsigned __int8)byte_41A144[0] >> 2];
v5 = v4 + 1;
*((unsigned char*)v12 + v5) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | (16 * (byte_41A144[0] & 3))];
*((unsigned char*)v12 + ++v5) = aAbcdefghijklmn[64];
*((unsigned char*)v12 + ++v5) = aAbcdefghijklmn[64];
v4 = v5 + 1;
break;
case 2:
*((unsigned char*)v12 + v4) = aAbcdefghijklmn[(int)(unsigned __int8)byte_41A144[0] >> 2];
v6 = v4 + 1;
*((unsigned char*)v12 + v6) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | (16 * (byte_41A144[0] & 3))];
*((unsigned char*)v12 + ++v6) = aAbcdefghijklmn[((byte_41A144[2] & 0xC0) >> 6) | (4 * (byte_41A144[1] & 0xF))];
*((unsigned char*)v12 + ++v6) = aAbcdefghijklmn[64];
v4 = v6 + 1;
break;
case 3:
*((unsigned char*)v12 + v4) = aAbcdefghijklmn[(int)(unsigned __int8)byte_41A144[0] >> 2];
v7 = v4 + 1;
*((unsigned char*)v12 + v7) = aAbcdefghijklmn[((byte_41A144[1] & 0xF0) >> 4) | (16 * (byte_41A144[0] & 3))];
*((unsigned char*)v12 + ++v7) = aAbcdefghijklmn[((byte_41A144[2] & 0xC0) >> 6) | (4 * (byte_41A144[1] & 0xF))];
*((unsigned char*)v12 + ++v7) = aAbcdefghijklmn[byte_41A144[2] & 0x3F];
v4 = v7 + 1;
break;
}
}
*((unsigned char*)v12 + v4) = 0;
return v12;
}
int main()
{
char a[] = "Hello World!";
printf("%s", (char*)unknown(a, sizeof(a)));
}
|
知道了这个函数的作用,
接下来只需要处理一下字符的移位就可以还原出原文了
1
2
3
4
5
6
7
8
| import base64
ciphertext = "e3nifIH9b_C@n@dH"
plaintext = ""
for i in range(0,len(ciphertext)):
plaintext += chr(ord(ciphertext[i])-i)
print(base64.b64decode(plaintext).decode())
|
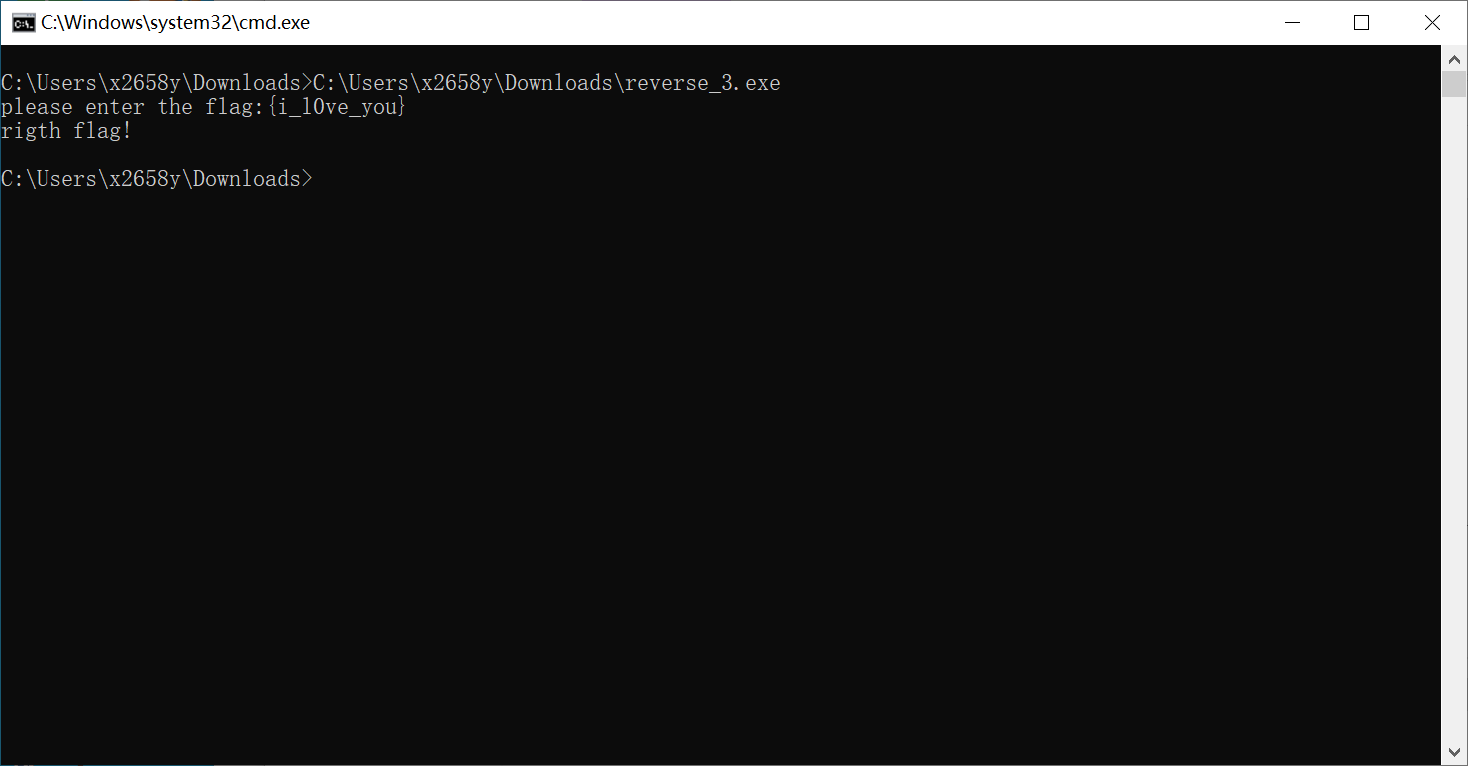
验证一下, 没毛病
 image-20220121230115616
image-20220121230115616